INTELLILINK Cloud Security Monitoring and Operation Service
What is INTELLILINK Cloud Security Monitoring and Operations Service?
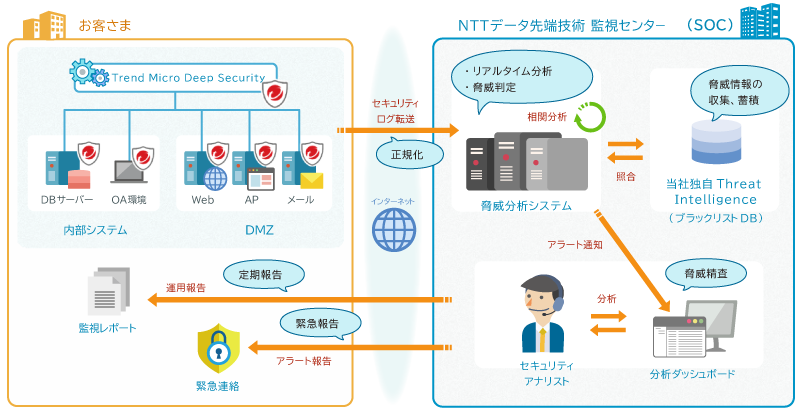
INTELLILINK Cloud Security Monitoring and Operation Service is a managed security service that utilizes Trend Micro Deep Security, a comprehensive server security product from Trend Micro, threat analysis engine that we have developed, and independently collected DNS blacklist.
Features of INTELLILINK Cloud Security Monitoring and Operation Service
- (1) We provide support from identification of cyber attack to recovery
When an incident occurs, we provide support up to the primary response. While such security measures require personnel with specialized knowledge and skills, "INTELLILINK Cloud Security Monitoring and Operation Service" provides one-stop support from cyber attack identification (identification of monitored targets and assets), prevention (access control and blocking), detection (malware and attack detection), and response (analysis and signature improvement).
- (2) We monitor the security same as in an on-premise environment with security products suitable for cloud environment.
"Trend Micro Deep Security" can comprehensively monitor servers regardless of environment such as on-premise or cloud so that the customers who are considering migrating to the cloud can monitor unauthorized access with the same quality as measures taken in the on-premise environment. Our security specialists, who are experienced in "Trend Micro Deep Security" provide one-stop services from initial installation including license procurement to product maintenance and security monitoring, facilitating safe and secure use of cloud to the customers.
- (3) We monitor security for 24 hours a day, 365 days a year
We monitor unauthorized access to customer systems 24 hours a day, 365 days a year. If we discover any unauthorized communication, we will make emergency contact by phone or e-mail. We will upgrade and tune the detection system as needed to respond to ever-changing cyber-attacks. This reduces the burden on customer to secure specialized security personnel and ensures a high-level of security.
- (4) We detect all the difficult-to-identify threats
Our security specialists can detect difficult-to-identify threats by performing correlative analysis of customer system security logs collected from "Trend Micro Deep Security" using our own threat analysis engine.
Customer Benefits of "INTELLILINK Cloud Security Monitoring and Operation Service"
- The pricing structure assumes the use in the cloud. We also provide the price structure for auto scale.
- Through interviews at the time of introduction, we propose the optimal operation level based on the actual operations of the customer, and provide security operations based on availability, confidentiality, and integrity.
"INTELLILINK Cloud Security Monitoring and Operation Service" Introduction Flow
| Hold a meeting and collect information | Monitoring preparation | Operation |
|---|---|---|
| Confirm the network environment of customer, information about the environment to be monitored, and contact information according to the content. | Set up the policy according to the results of the interview, verify the operation, and test the connection with the security monitoring center. | Provide emergency reporting of alerts affecting the system, present reports, update signatures, and perform tuning. |