Exabeam, a user and equipment behavior analysis solution
What is UEBA "Exabeam"?
As seen in many targeted attacks recently, the threat of information leakage, risk of not being aware of damage and risk of attack hampering the entire infrastructure have increased with rise in cases of advanced security attacks and internal fraud. Cyber-attacks are evolving daily, and it is not practical to prevent all of them.
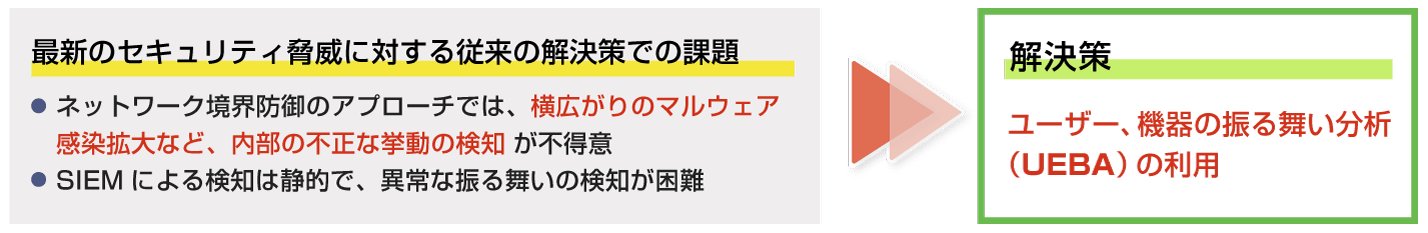
Traditional "ingress/egress" approaches to protecting the boundary between the Internet and internal networks are not good at detecting internal compromise behavior, such as the spread of malware on internal networks. In addition, the existing correlation analysis solution SIEM (Security Information and Event Management) is mainly based on static detection, making it difficult to detect new attack methods.
This requires not only network boundary defense and existing SIEM approaches to detection, but also countermeasures to enable detection after an attack has penetrated the internal network.
Exabeam is a User and Entity Behavior Analytics (UEBA) solution, a next-generation SIEM that can detect new threats by detecting and visualizing abnormal behavior seen in targeted attacks and internal fraud.
Like conventional SIEM products, it centrally accumulates and manages logs of the operating status of various equipment and software, and can also understand the operation pattern of users and equipment through machine learning in addition to detecting threats to the internal network as quickly as possible.
*1 NIST Cybersecurity Framework Version 1.1 document link
https://www.ipa.go.jp/files/000071204.pdf
Features of Exabeam
- [1] Advanced detection and analysis functions
-
- Correlation analysis using machine learning enables detection of sophisticated attacks and internal frauds that are difficult to detect using existing products.
- You can aggregate and analyze logs from major services and devices, from cloud to on-premises.
- [2] Operational efficiency
-
- Timelines for each user are automatically created, allowing quick post-detection analysis and response.
- The user interface is designed to make it easy to understand security incidents even for those with limited expertise.
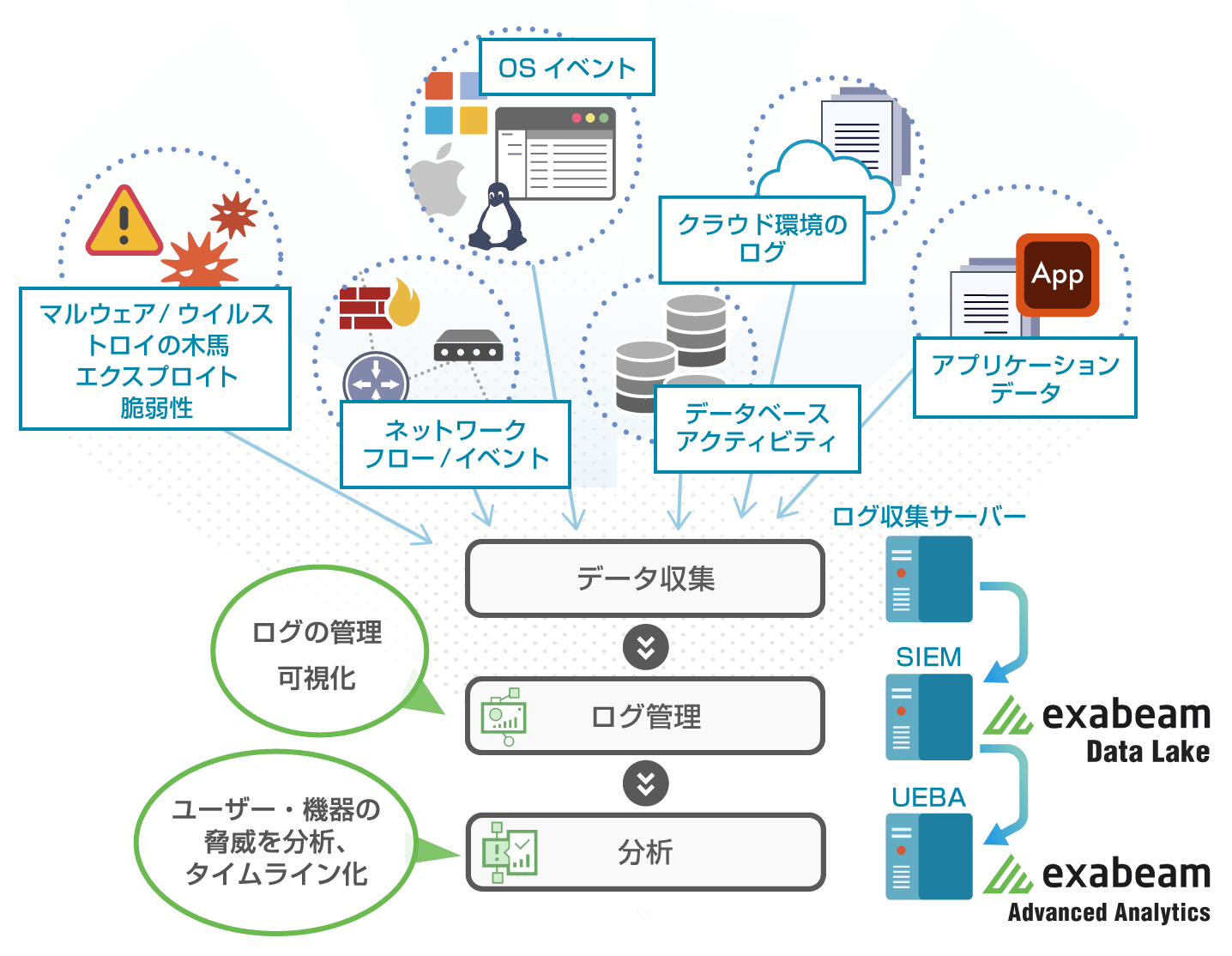
(Figure) Exabeam Implementation
Exabeam Data Lake (log management server) enables visualization using log management and reporting functions, and Exabeam Advanced Analytics (log analysis function) collects event data and network flow information and dynamically performs correlation analysis. Exabeam Advanced Analytics automates management and analysis, including user and device behavior, to quickly identify problems.
Flow of Implementation of Exabeam
We provide one-stop service from design and construction to implementation, maintenance, tuning, and monitoring operations.
| Hold a meeting and collect information | Construction | Service Offerings |
|---|---|---|
| We interview the client about the client's network environment and environmental information to be logged. | We design the system based on the information gathered in the interview, and construct, install, and test the log aggregation server and Exabeam devices. | Our security experts are available to provide support for rule tuning and continuous 24/7 monitoring where necessary. |