Access Log Monitoring Tool ALog ConVerter
This is a type of access log audit tool that obtains "access log storage" from the server, which is essential as an audit trail.
ALog ConVerter®is an all-in-one packaged software with functions for "collection", "compressed storage", "search", and "analysis" of operation log history, such as file access and login to servers.
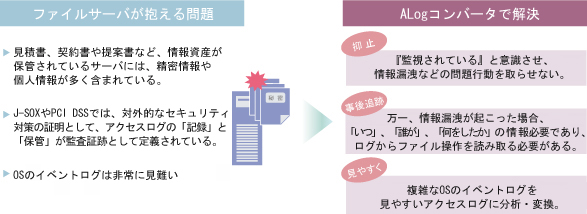
What is the importance of log in a file server?
Recording and storing access log trails for servers has become a mandatory requirement under security guidelines, PCI DSS, and other laws and standards. However, it has been practically impossible to centrally store and manage logs in a server environment accessed by a large number of users until now. Log-on/log-off logs alone are not sufficient for tracking incidents and accidents such as information leakage because it is necessary to know "who did what and when". It is necessary to be able to read file operations from the log.
Features and Functions of ALog Converter
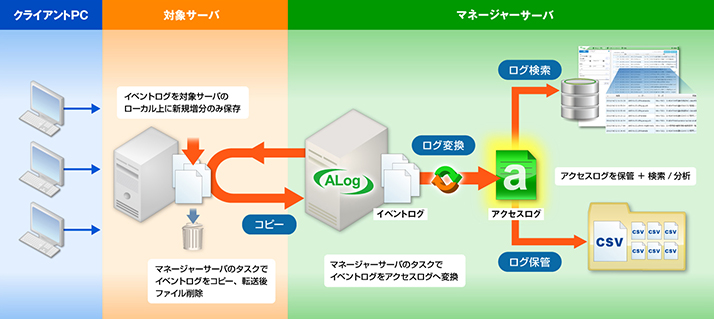
ALog ConVerter utilizes OS event logs to generate access logs (operation history). It acquires event logs from the target server, copies and transfers them to the ALog server, and performs analysis conversion or compressed storage/search/analysis of the logs on the ALog server side. This product does not place a burden on the target server or network and is compatible with a large number of servers. It is also easy to install and simple to operate, making it efficient even for small users.
- 1. No burden on the server
- Resident software is not installed on the PC or target server, so the existing environment is not affected.
- 2. No work on client PC
- Agent installation is not required.
- 3. Unauthorized access alert function
- If "unauthorized access" is defined in advance, the administrator can be notified by e-mail when an unauthorized access operation actually occurs.
- 4. Extensive experience of installation
- It has been installed in more than 3,000 companies in the various industries such as information/communications, finance/insurance, manufacturing, public sector, and construction/real estate.
*Results as of April 2018.
Types of logs obtained by ALog ConVerter
- File Access Log
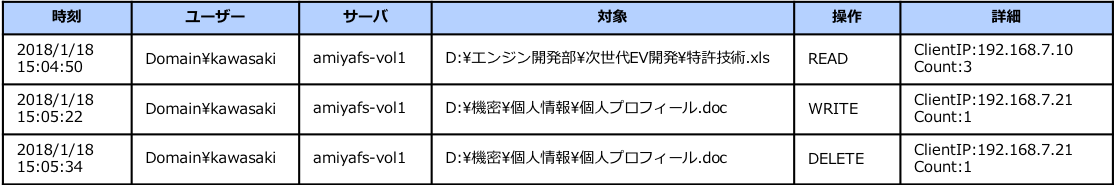
- ALog ConVerter keeps a history of access to files on the file server, converted into a visually understandable format. Also, by passing a log formatting analysis program, it is possible to output more accurate operation patterns than the original event logs.
-
- Login log
- ALog ConVerter converts and stores the history of user logins to a domain or machine. It is possible to know when the user authenticated Windows (= booted the PC) and to check the user's IP address from the log.
- Administrator operation log
- ALog ConVerter keeps record of operation history related to security policy settings such as "creating user accounts" and "changing password", which are performed by the administrator.
*A history of changes to domain security policy from AD server and local security settings from other servers can be obtained. - Access rights modification log
- ALog ConVerter keeps the log of changes to folder/file permissions.
- Print log
- ALog ConVerter keeps converts and stores printing history of print server. It keeps a record of "when", "who", "which file", and "how many pages" were printed.
- Logoff log
- ALog ConVerter keeps log of successful and unsuccessful user logoff. Information on "when", "who", "from which IP", and "logoff/shutdown" can be obtained from this log. Logoff is captured, converted and stored in ALog using a logoff script because the information from the event log is not useful.
- Process start and end log
- ALog ConVerter converts and stores logs of process start and termination history (program execution history) from each target server. CREATE is mention in the operation column for process start and creation, and EXIT is mentioned in the operation column for process termination. The log maintains a record of "when", "who", "processes in which file path", and "were started/created, terminated".
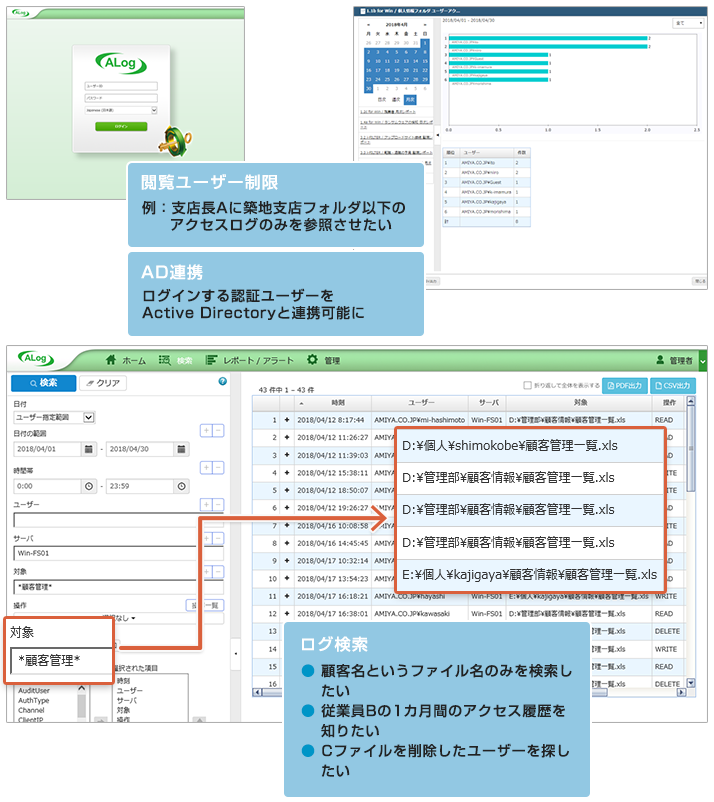
Access Log Search System
In addition to the conventional search function, various other functions such as management functions, graphical representation of statistical aggregate data, automatic report generation have been added.
- Aggregate function
-
- File Access Ranking
- User Access Ranking
- Total file access (by time, by day of week, by date)
- Aggregate function automatically generates aggregate graphs and result files for these. Report definition can be self-generated.
- Monitoring report function
-
- If unauthorized access is defined in advance, the system will generate a file as a report as well as an alert e-mail notification.
--- Usage Example ----
- "If a user fails to login 10 times in a day, output it in the monitoring report"
- "If there is any access during the late night (22:00 to 6:00), output it in the monitoring report"
- "Create a report for the entire operation history of a prospective retiree"
- "Create a report for users who log off after 9 p.m."
*Specify conditions such as user name, file name, and operation pattern to narrow down the search. Audit reports can be generated automatically.
Search and monitoring aggregate report screen
Hardware conditions
For more information, please see the following page.
-
Server access log ALog ConVerter operating environment and price (external site)
https://www.amiya.co.jp/solutions/alog_converter/spec_price.html?id=spec_price_ttl-common
*ALog ConVerter is a registered trademark of Amiya Corporation.
*All other company names, product names, service names, etc. mentioned herein are trademarks of their respective owners.