INTELLILINK SIEM Security Monitoring and Operation Services
Need for SIEM
SIEM (Security Information and Event Management) is a product that centrally manages security events and logs and performs cross-sectional analysis to detect, analyze, and visualize traces and signs of unauthorized access that cannot be found by security devices alone.
In order to understand increasingly diverse and complex threats and implement prompt countermeasures, there is a growing need to deploy various security devices and SIEMs that collect, correlated and analyze logs from these devices in real-time.
Service Features
In order to effectively utilize SIEM, it is necessary to analyze and manage the system based on an understanding of the overall picture of one's own organization system, and it is necessary to have an SIEM team skilled with the latest security knowledge and know-how.
We have an extensive experience in SOC operation since 1997 and a track record of providing services through SOC to many companies and organizations, including government agencies and financial institutions. We leverage the know-how we have accumulated over the years to provide a one-stop support for SIEM infrastructure implementation at our clients' sites—from planning to construction and operation.
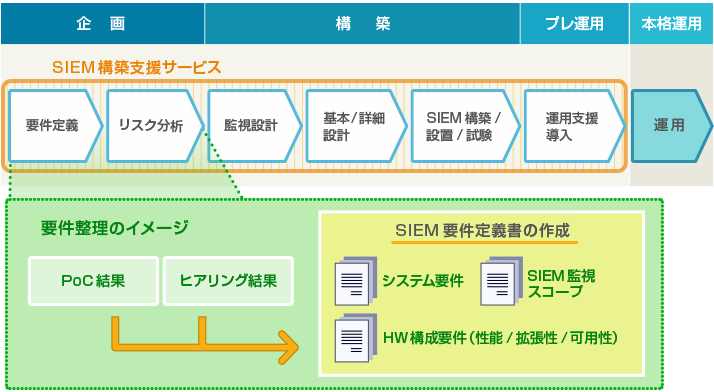
*The above figure gives an example of the flow of SIEM construction. We propose the best ways to proceed according to the client's organizational structure and system environment.
PoC (Proof of Concept): PoC in SIEM implementation refers to the phase wherein SIEM system is installed and evaluated to verify the detection/analysis effects and equipment sizing conditions after installation prior to implementation so that the actual implementation can be carried out smoothly.
Example of service implementation
INTELLILINK SIEM Security Monitoring and Operation Service provides the following support in response to client requests.
| Item | Details |
|---|---|
| Requirement defining | Tasks related to interviews/detailing of functional and non-functional requirements |
| Risk analysis | Tasks necessary for defining the SIEM monitoring targets, such as checking the status of client assets, assuming breach patterns, and defining the risk patterns to be detected |
| Monitoring design | Review of monitored devices and logs, verification of detection methods and design/implementation of SIEM detection rules, creation of custom SIEM parser |
| Basic/Detailed design | System design for SIEM equipment construction and installation |
| SIEM construction/installation/testing | Construction of SIEM equipment, and installation and testing of equipment in the client environment |
| Assistance in implementation of operations | Assistance in operational design, documentation of operation and establishing operation (simple training) when SIEM is operated by the client |
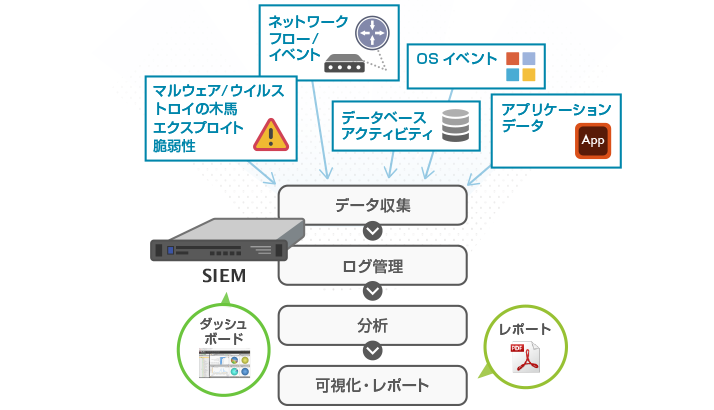
(Figure) SIEM Application
By utilizing SIEM, information obtained from various security products, operating systems and applications can be centralized, and log information obtained from devices other than security devices can be combined for information visualization and cross-sectional analysis, making it possible to understand various threats.
How is INTELLILINK SIEM Security Monitoring and Operation Service Beneficial to the Clients?
Our engineers with expert knowledge provide assistance in each phase necessary for implementation of SIEM infrastructure according to client's needs. Outsourcing of SIEM construction reduces the client's workload and security costs.
Flow of INTELLILINK SIEM Security Monitoring and Operation Service
| Planning | Construction | Deliverables |
|---|---|---|
| Conduct interviews, define requirements, perform risk analysis and PoC, and prepare monitoring design and basic design. | Prepare a detailed design in accordance with the results of the interviews, and implement SIEM construction, installation, and testing. | Prepare requirement defining document, monitored threat list, monitoring method design document, basic design document, parameter sheet, test result report, etc. as needed. |
Related Services
*All other company names, product names, service names, etc. mentioned herein are trademarks of their respective owners.