INTELLILINK Threat Hunting Services
Our security analysts find traces of intrusion and support "offensive security measures".
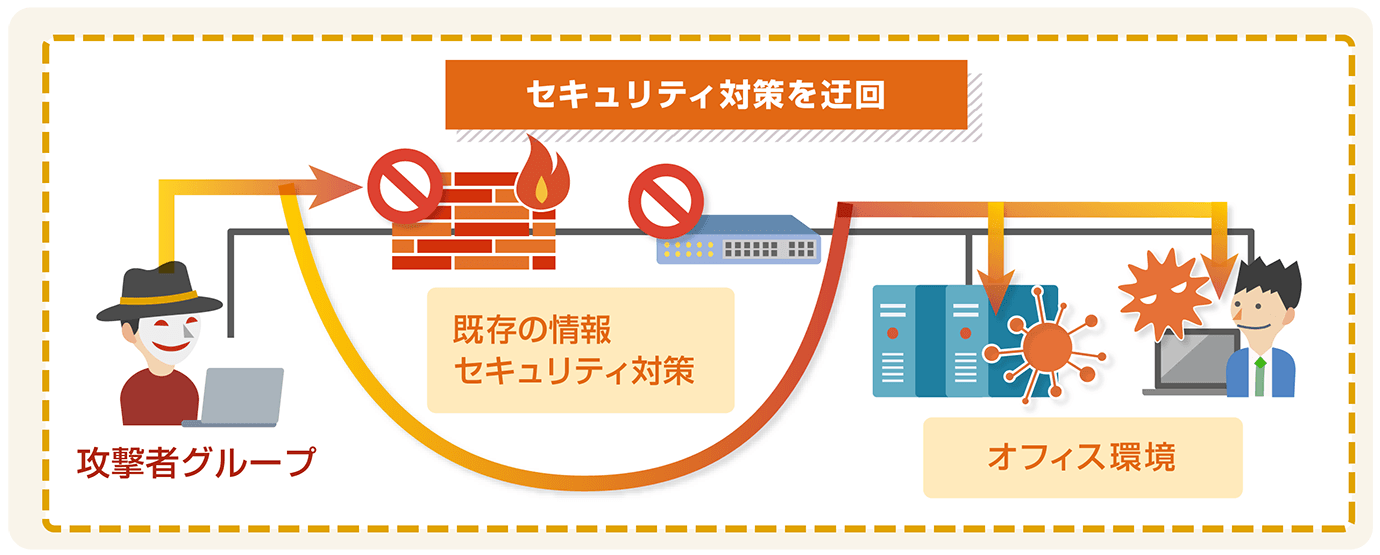
With cyber attacks and insider threats becoming more complex and serious these days, the environment surrounding companies is changing, and it is difficult to completely prevent attacks. Sophisticated cyber attackers, such as APT attacker groups suspected to be state-sponsored, will try to circumvent existing information security measures and make inconspicuous attack. When targeted by such attackers, it is not easy to find traces of the intrusion inside IT systems.
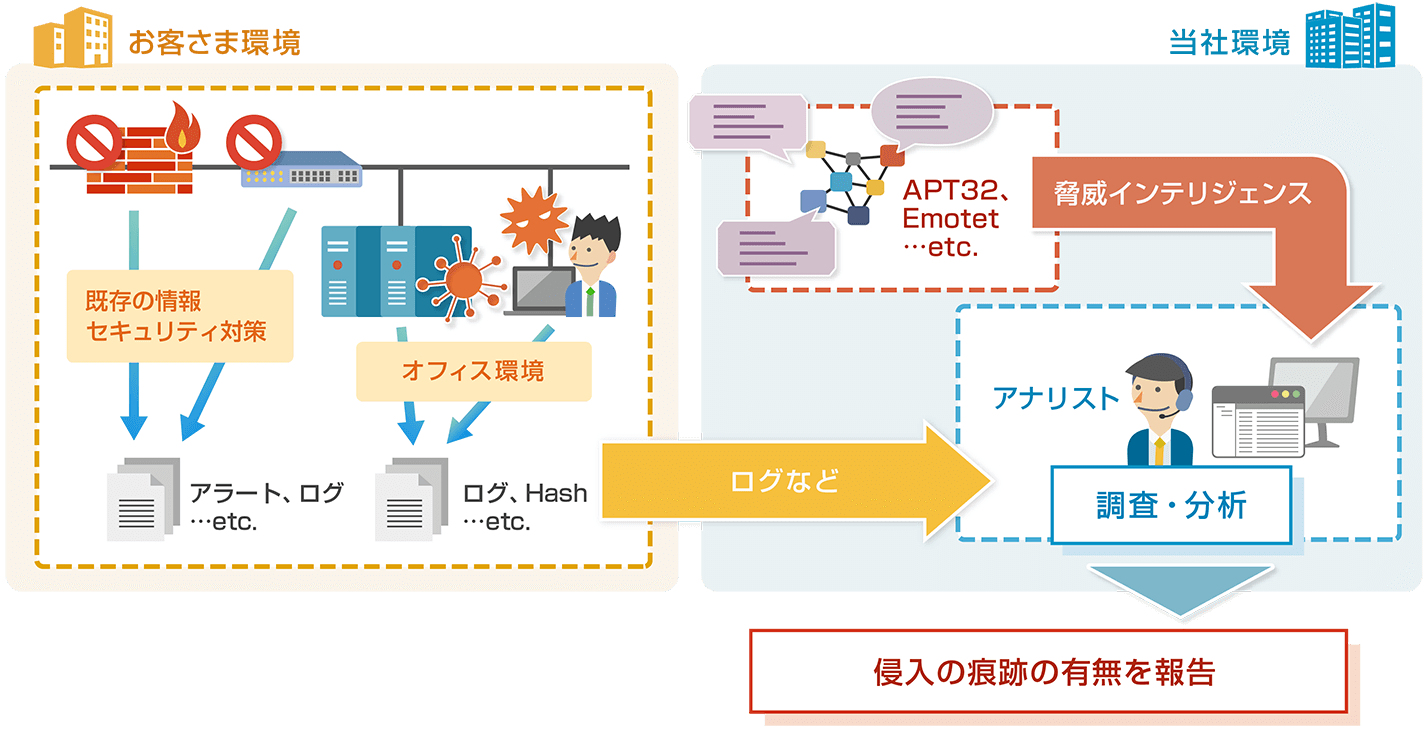
Overview of INTELLILINK Threat Hunting Service
The "INTELLILINK Threat Hunting Service" provides customer information security measures by having analysts investigate and analyze whether there are traces of advanced threats based on the latest threat intelligence that we possess as a security service provider.
This service enables active investigation of the inconspicuous activities that attackers are conducting to circumvent existing information security measures. This prevents continuous breaches and reduces damage.
Our Strengths
Use of latest and unique threat intelligence
We accumulate the latest threat intelligence through CSIRT activities and information collaboration within the NTT Group. We also accumulate unique threat intelligence by analyzing the attack patterns of various forms of attacker groups, such as state-sponsored, money-oriented, and hacktivists. These threat intelligence can be used to investigate and analyze the traces of various types of intrusions.
Analysts with extensive incident response experience
We have been providing incident response services to our customers for some time, and analysts with extensive experience in incident response who have knowledge in digital forensics and malware analysis will conduct investigation and analysis in this service.
When data requiring urgent response, such as threat intrusion, is identified, it can be reported immediately and responded to as an incident response service.
Service Flow
| Receive Order | Kickoff | Investigation | Reporting |
|---|---|---|---|
| We agree on the threats to be investigated in the customer environment. | Based on the agreed threats, we will request information (such as logs) to be obtained in the customer environment. | Based on our accumulated threat intelligence, our analysts will investigate and analyze whether there is any evidence of advanced threats intruded in your IT system environment. | We will prepare and provide a report summarizing the results of the investigation. |